Review Article Open Access
The Role of Protection Measures and their Interaction in Determining Building Vulnerability and Resilience to Bioterrorism
Taylor J1, Margaritis D1, Nasir ZA1, Borrion H2 and Lai KM1,3*
1Healthy Infrastructure Research Centre, Department of Civil, Environmental and Geomatic Engineering, University College London (UCL), London, UK
2UCL Department of Security and Crime Science, London, UK
3Department of Biology, Hong Kong Baptist University, Kowloon Tong, Hong Kong
- *Corresponding Author:
- Lai KM
Department of Biology
Hong Kong Baptist University
Kowloon Tong, Hong Kong
E-mail: Laikaman@hkbu.edu.hk
Received Date: December 31, 2012; Accepted Date: February 05, 2013; Published Date: February 08, 2013
Citation: Taylor J, Margaritis D, Nasir ZA, Borrion H, Lai KM (2013) The Role of Protection Measures and their Interaction in Determining Building Vulnerability and Resilience to Bioterrorism. J Bioterr Biodef 4:123. doi: 10.4172/2157-2526.1000123
Copyright: © 2013 Taylor J, et al. This is an open-access article distributed under the terms of the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original author and source are credited.
Visit for more related articles at Journal of Bioterrorism & Biodefense
Abstract
Understanding the risk presented to buildings by bioterrorism has been a topic of research interest in recent years. Risk assessment methodologies and guidelines for the protection of buildings have been developed by a number of researchers, but it remains difficult to quantify the vulnerability and resilience of a building. It is an important issue from both biosecurity investment and operation point of view because different measures have different cost and operation implications. This paper reviews existing risk assessment methodologies, introduces a novel framework for classifying protection measures, and determines the inter-relation of the framework components and building vulnerability and resilience using a fault tree analysis within a biosecurity network system. Future work will develop weighting values for the different protection measures within the framework, allowing for the calculation of bioterrorism resilience of existing buildings, and to provide a decision making guide for building architects, builders, and managers for new and retrofitted buildings.
Keywords
Bioterrorism; Indoor environment; Protection measures; Building vulnerability; Biosecurity assessment
Introduction
Bioterrorism refers to a malicious attack using biological agents with the aim to cause casualties and fear amongst the targeted population. Following the anthrax attacks in the U.S. in 2001, there has been an increased focus on understanding the risks from bioterrorism to buildings. The attack had major repercussions, with the death of five individuals, the infection of another 17, and total costs reported to exceed $1 Billion [1]. It has been known that Al Qaeda has long sought to obtain biological and chemical weapons, and has made attempts to develop such weaponry itself [2]. In addition, the global spread of biotechnology and varying standards in laboratory security mean that the knowledge and technology is becoming more widely available to potential terrorists. Instability in countries which may have researched and developed biological weaponry may also lead to BWA (Biological Warfare Agents) being acquired by terrorists.
Understanding the risk of a bioterrorist attack on a building requires information about the nature of the threat and the vulnerability of the building to an attack. Assessing the threat to buildings requires difficult to acquire information about the nature of the threat, while the design of buildings can help reduce the vulnerability to attack, or the number of individuals infected following an attack, through the implementation of a series of protection measures that can be implemented prior to, in the event of, and following the bioterrorism event. A range of different protection measures in the form of engineering and biological systems can be put in place in new and existing buildings to help control the risk of bioterrorism to building occupants.
In this research, bioterrorism will be considered for commercial office buildings, with the building occupants as the target population. The objective of this research is to introduce a novel framework for the assessment of the vulnerability and resilience of different buildings to a bioterrorist attack, and to demonstrate the relative importance of protection measures within the bioterrorism resilience framework. Different types of protection measures will be described, and their interrelation based on the spatial and temporal sequence of a bioterrorist attack will be mapped using a fault tree analysis within a biosecurity network system. This work will help to improve the quantification of the vulnerability of existing buildings, and provide information to architects, builders, and building managers on how best to protect their buildings from, during, and following an attack.
Review of Risk Assessments and Developing a Protection Measure Framework
A biological attack uses BWA including pathogens (diseasecausing agents) and biotoxins (poisonous substances produced by a living organism), to cause illness and death, psychological turmoil (e.g. fear and anxiety) and economic and social instability to the rest of the society. Examples of BWA are fungi, bacteria, viruses and biotoxins. The pathogenicity of the BWA, the mode of contaminant delivery, and the behavior of the BWA in the indoor environment are all considerations when examining the risk to a building and evaluating the effectiveness of protection measures.
BWA can be introduced to a building as a surface contaminant on an object (fomite) or food, as a bioaerosol or powder designed to spread through the indoor air of the building, or through the water supply. BWA may enter the property through leakage following an outdoor release, through the air intakes or air handling unit, through a terrorist entering the building and releasing the BWA, or through the delivery of a contaminated piece of mail or package. The behavior of the BWA in the indoor environment will depend on the initial levels of contaminant released, the physical and biological decay of the pathogen in the environment, and the movement of the contaminated air throughout the building.
The physical decay of BWA in the indoor environment refers to the loss attributable to physical factors such as unrestricted diffusion, surface impaction, and fall-out. Unrestricted diffusion allows the movement of aerosolized particles out of the zone where the pathogen was released into other areas within the building, or the external environment. This dilutes the concentration of the particle in the indoor air, but can also lead to the spread of the pathogen to areas of the building not directly targeted. Surface impaction refers to the attachment of contaminants to surfaces, while fall out refers to the deposition of the contaminant particles on surfaces due to gravity. Physical decay does not necessarily eliminate the threat, but may remove it from the indoor air, although the risk of re-suspension can remain.
The biological decay of BWA within the built environment depends on the type of pathogen, and the surrounding environmental conditions. Potential pathogens used in bioterrorism can exhibit a range of survival times in the environment. The persistence of pathogens is dependent on environmental conditions, including the temperature and relative humidity of the indoor environment and solar radiation levels [3]. Fungi and some bacterial species, for example Anthrax, can form spores, allowing them to survive desiccation and remain viable for years. The nature of the BWA and the means of delivery of the contaminant to the building will dictate the threat and the consequences of an attack.
Threat analysis for buildings
A successful bioattack on a building will be a product of a number of factors, including the terrorists’ resources, capabilities, and decisions, actions by other individuals and/or groups, and the buildings resilience. Assessing terrorism risk in specific buildings is often considered to be a combination of the threat of an attack, the vulnerability to the attack, and the expected consequences of theattack.
Risk = threat ×vulnerability ×consequences
Threat assessments for buildings to a bioattack consider components such as the attractiveness of the building as a target, the adversary’s motivation, intent and capability, and the mode of attack in order to evaluate the likelihood of specific incidents; vulnerability is influenced by the prevention and detection systems in place; and consequences typically relate to the infections, deaths, and financial and operational costs incurred by an event [4].
Risk models: Estimating the risk of an attack on a target is near impossible; variations in the pathogenicity and environmental behavior of the BWA, the defenses and resilience of the built environment, the mode of delivery, and the behavior and intentions of the terrorist all impact the consequences from an attack. There are a vast number of potential bioattack scenarios, making it impossible to predict and prepare for all possible bioterrorism events [5]. Furthermore, there is little data that can be used to estimate the risk of bioattack as there have been few historical cases on which to base models; there is a likely low rate of future attacks that could allow for model calibration or validation, and information on the intent and capabilities of terrorists is difficult to obtain [6].
While the number of parameters required to create a global terrorism risk model are prohibitively large, there have been a number of attempts to characterize the risk of a bioattack on a specific target. Kowalski describes a methodology for determining the risk of a chemical or biological attack faced by a building relative to other buildings [7] that predicts the risk to the building based on risk factors such as hazard, occupancy, profile, and vulnerability, and uses estimates of these risk factors to determine the risk of attack. A risk analysis has been proposed by Zilinskas and colleagues which would include a primary qualitative vulnerability assessment followed by a risk estimation based on a quantitative process [6]. Another quantitative methodology for assessing risk to buildings from a bioterrorism event was proposed by Reddy and Fierko [8], who examined the problem from the point of view of building owners and managers, assessing the risk of casualties and the impact on building operations and financial costs of an attack. Radosavljevic and Belojevic [9] proposed a model of bioterrorism risk assessment that examined perpetrators, BWA, means or media of delivery, and targets as the components of an attack, while Radosavljevic and colleagues have also proposed a quantitativemodel of Bioterrorist Attack Risk Assessment [10]. The target component of an attack includes building vulnerability, and has both qualitative (e.g. control of air, parameters of protection) and quantitative (e.g. number of people in the target) parameters. Ezell and von Winterfeldt suggest using probabilistic risk analysis to quantify bioterrorism risk [11].
Vulnerability assessments: While determining the risk to a facility from a bioterrorist attack is difficult, the understanding of the factors that can influence infection control in the built environment is well understood, meaning that vulnerability analyses can be generated based on experience in indoor air quality studies and crime scripts.
A number of different guidelines are available to the public in order to help architects, builders, and building managers reduce the potential impact of a bioattack with recommendations on the design and operation of buildings. The National Institute for Occupational Safety and Health (NIOSH) in the U.S. has published guidelines for protecting buildings from airborne Chemical, Biological, and Radiological and Nuclear (CBRN) attacks [12] as well as Heating, Ventilation, and Air Conditioning (HVAC) system-specific recommendations [13]. The Lawrence Berkley National Laboratory has developed guidelines for safeguarding a building against chemical or biological attacks [14] for emergency workers and building operators. The American Society of Heating, Refrigerating, and Air-Conditioning Engineers (ASHRAE) have produced risk management guidelines for extraordinary incidents, CBRN attacks [15]. The U.S. Army Corps of Engineers and the U.S. Army Soldier and Biological Chemical Command have also produced documents detailing how to protect buildings from airborne hazards [16,17]. The National Institute of Standards and Technology (NIST) in the U.S. has published a document named ‘Cost-Effective Responses to Terrorist Risks in Constructed Facilities’, [18] for risk mitigation in constructed facilities. Finally, the Federal Emergency Management Agency (FEMA) in the U.S. has produced a guide for the mitigation of potential terrorist attacks, including biological attacks, on buildings [19] and the U.S. Department of Defense has published minimum antiterrorism standards for buildings [20]. While these guidelines can be used to understand the technologies and systems that can be used to protect a building, they cannot be used to accurately calculate the overall vulnerability of a building to a bioattack.
Researchers have also produced tools for the assessment of the vulnerability of buildings to bioterror attacks. A systems dynamic methodology has been proposed and demonstrated by Thompson and Bank [21] as a decision-making tool for building design and operation with regards to a bioterror attack. The BVAMP (Building Vulnerability Assessment and Mitigation Program) software can be used to assess the vulnerability of a building to a CBR attack, and propose recommendations for the improvement of the buildings resilience, while taking into consideration the costs and energy requirements of improvements [22]. The Chemical/Biological Building Protection Tool (CBT) is another checklist based software package, which evaluates vulnerability, and provides guidance [23]. Documents which can be used to assess a building’s resilience through the use of checklists include the HVAC Building Vulnerability Assessment Tool, which was developed by the Rhode Island Department of Health in order to locate the vulnerabilities of an HVAC system to a biological attack [24], and the Building Assessment Checklist created by the County of Los Angeles Public Health Department [25]. However, these checklistbased systems are not capable of calculating the overall vulnerability of a building, and do not take into account the inter-relation of different protection measures.
Models for assessing the vulnerability of buildings to bioterror that account for the inter-relation and relative risk of failure have been proposed. The fault tree analysis model of Hope [26] for bioterrorist risks to the U.S. food supply has been suggested to be applicable to scenario modelling for attacksinvolvingbuildings [6]. Fault tree analysis is a means of analysing a system using Boolean logic to determine the probability of a specific system failure. A conceptual framework for determining the vulnerability of a building in terms of a probabilistic, relative risk-based decision methodology has been proposed by Reddy and Bahnfleth [27]. The primary difficulty in determining the level of risk to a building is producing estimates of the risk level for the different risk factors; the probabilities of failure of the building protection measures against a bioattack are largely unknown, making such a model difficult to calibrate.
Despite the efforts to produce guidelines for building vulnerability assessment, there remains little quantitative data that describes the efficiency of the different protection measures that exist in buildings, nor have the relative importance and spatial and temporal interaction between the protection measures been described. Therefore, a biosecurity network system which describes the different types of protection measures and their inter-connections is an important first step towards a standard building vulnerability assessment for bioterrorism risk calculation and evaluation of the value, added value and redundancy of a protection measure in a network system.
Protection measures and categorization framework
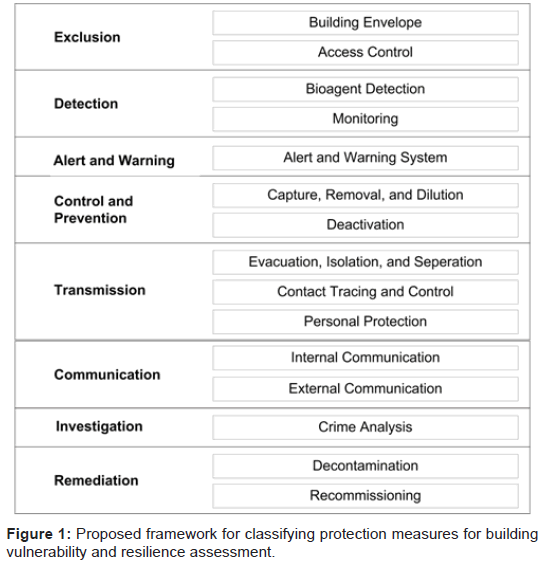
Understanding BWA behavior in a building and its effect on the population within the building is critical to minimizing the casualties following an attack. Reducing the vulnerability of a building to an attack, or the number of individuals infected following an attack, can be achieved by a series of protection measures that can be implemented prior to, in the event of, and following an attack. Analyzing the above literatures and the current practice and management in the field of fire safety [28,29] and biosafety and biosecurity in laboratories [30], Figure 1 is proposed in this study to describe the various protection measures that can be implemented within a building that can impact the vulnerability and resilience of the building. Engineering and biological systems can be put in place in new and existing buildings to help eliminate or reduce the threat of bioterrorism to building occupants. The different potential protection measures are introduced, and their importance discussed.
Exclusion: The ability to prevent a bioterrorist attack on a building will be intrinsically linked to the ability to exclude BWA or individuals intent on deploying BWA from gaining access to the building. Aerosolized pathogens are one of the primary means of disease transmission, and restricting external access to ventilation intake locations in the building envelope is crucial for preventing the release of an airborne BWA into the indoor environment [7,13]. This includes locations for both natural ventilation such as windows, as well as inlets for active ventilation systems such as HVAC systems. Windows and inlets should be located so that they are not easily accessible for BWA to be placed or thrown into.
The permeability of the building structure may impact the resilience of a building to a bioattack. A highly permeable building will be susceptible to contaminant penetration across the building envelope, while an airtight structure may prevent BWA released inside the building leaving through natural air changes. Air barriers can be used in the building construction to reduce permeability of the building envelope and help prevent any BWA deployed outside the building from moving into the building [14,16].
Access control methods can restrict access to vulnerable locations within the building and help to prevent malicious individuals or hazardous packages gaining access and BWA being released or deter an offender from attacking a vulnerable location in the building. Access should be restricted to those with security clearance, and packages should be checked before being re-routed within the building. Access control can be enabled through the use of high-security access cards, locked doors, security guards, and external mail screening systems [16,30].
Detection: The detection of pathogens and suspicious incidents and activities related to the release of pathogens in the indoor environment can be achieved through building surveillance, BWA detection, and environmental detection [7,12,14,16,17,30]. Detection measures for BWA can range from the generic to the BWA-specific, and can be used before, during, and after an attack to monitor the environment and determine the nature of the threat.
The most basic form of detection is through surveillance by security personnel. Building surveillance can involve monitoring the building environment for suspicious behaviors, substances, or medical issues arising in the building occupants. Security staff and facility managers can be trained to recognize the signs of a bioterrorist attack, and be able to react accordingly. Surveillance mechanisms are generic protection measures that are non-specific to bioattacks, but can play a vital role in protecting infrastructure. However, the performance of this measure is related to the training of the security staff and may lead to a high number of false alarms due to the inability to identify specific substances that may or may not constitute a threat.
Specific BWA detection methodologies can focus on sampling either environmental surfaces within the building or the indoor air. The ability to detect BWA in the indoor environment is a valuable tool in bioterrorism prevention, and has been an area of significant investment and research. Environmental sampling of indoor air and surfaces has been widely used to identify microbial contaminants within the built environment; however traditional analysis requires access to a laboratory and time to process the samples. Detect-to warn or detect-to-isolate systems require sensors which are capable of rapidly identifying contaminants in a matter of minutes, and can provide warnings for building occupants or control systems while minimizing false positives. Detect-to-treat systems are not capable of alerting building occupants to an attack, but can be used to inform the treatment of exposed individuals. Specific BWA detectors are still largely in the research and development phase, and are not yet able to provide detect-to-warn or isolate systems for building security due to the range of timescales required to identify the contaminant [31].
Biosensors can be generally classified as being sequence-based, structure-based, chemical-based, or function-based detectors [32]. Sequence-based detection systems analyze the RNA or DNA from pathogens to identify the species, and are sensitive to low levels of pathogen, have low false positive rates, but typically take 15 to 60 minutes to perform the analysis, meaning that the pathogen may already have spread throughout the building by the time it has been identified. Structure-based detection methods are capable of detecting the shape and distribution of biomolecules (e.g. antigens) on the surface of biological contaminants, and use these characteristics to identify the specific pathogens. Generally, structure-based detection is performed using an immunoassay, where specific antibodies are used to identify pathogens. Detection time can take as short as two minutes, allowing for a fairly quick detection of contaminants species; however insufficient specificity and non-specific binding may lead to false positives. Chemical-based detection relies on the detection of the molecular characteristics of biomolecules to detect pathogens, rather than biological activity. This methodology includes, for example, mass spectrometry [7]. The ability of these detectors to detect specific pathogens in complex mixtures of ubiquitous microorganisms is unknown. The spectral profile of the samples can be used to identify contaminants based on their known characteristics, meaning the system is only applicable for known BWA. Function-based detectors work by using whole organisms, cells, or cellular components to detect pathogens. Functional systems can detect unknown BWA, and provide a result within minutes to hours – a response time limited by the behavior of the detecting biological sample. The advantage of functional systems lies in the ability of the detector to identify unknown pathogens, and is not required to be pathogen specific [7].
Non-specific BWA detection involves using nonspecific point detectors to analyze particles within the indoor air, recording the count, size, shape, and spectral signature of aerosols. Such systems allow for the rapid analysis of indoor pollution levels, but cannot be used to distinguish specific contaminants from each other. Biological and non-biological particles can be distinguished from each other based on the light absorption and fluorescence of the particles. Nonspecific detectors are the only system available that provides true realtime information on bioaerosols, but are unable to identify the BWA and is likely to operate with a large number of false positives. Like with specific sensor, non-specific sensors can act as a disruption measure for a bioaerosol attack. Bayesian modeling using inputs from a number of different sensor types has been suggested as a method for improving the characterization of a release [33].
Alert and warning: Alert and warning systems: A detection system must provide a rapid warning of the release of BWA into the indoor environment, while minimizing the number of false positives and negatives. The need to maintain a central monitoring system for biosensors placed at strategic locations throughout the building is necessary in order to monitor the building for bioattack. Like with biosensors, the development of full networks of alert and warning systems for bioattack is still in the research and development stage. Such systems will be able to provide information on the movement of pathogens throughout a building, allowing security staff and building engineers to collect information and take action to prevent the spread. A network of sensors would act as a measure for information collection and analysis. Actions following alert and warning should be planned beforehand, and if it is suitable, the relevant measures should be designed in the building as part of a network system to ensure a rapid and well planned response [15,16,19].
Control and prevention: Controlling the movement of BWA around a building and preventing further spread and transmission will require knowledge of the airflow within the building environment. Aerosolised BWA may be removed from targeted buildings by dilution, filtration, or deactivation. This can be performed through the ventilation system in place, or by individual units installed throughout the building.
Dilution: The design of the HVAC system can act to prevent transmission of the pathogen throughout the building while helping to dilute the concentration of BWA inside the building by replacing contaminated air with fresh air [7,13]. Ventilation systems deliver varying amounts outdoor air into buildings, depending on the system design and often the location in the building. A system design with significant mixing between air handling zones may lead to transmission of the pathogen throughout the building. As such, mixing should be minimized, allowing for the HVAC system to isolate locations within the building and prevent pathogen transmission. Using the fan and damper functions of an HVAC system can also play an important role in defense. By using fan-system zonings, and altering the supply, return, and pressurization fans, engineers can help to prevent the spread of a BWA in the air through the building. In addition, emergency redundant HVAC systems can be put in place to help control air flow. Dilution of the contaminants in the indoor air is an effective way to reduce the contaminant level within the indoor air. Many HVAC systems have smoke purge fans, which can be activated in the event of an emergency to rapidly ventilate the building, clearing out the indoor air.
In many cases, the best response to a bioterrorist attack may be to shut down the HVAC system to prevent distribution of the BWA to different areas within the building. In cases of buildings without HVAC systems, ventilation can be increased by opening windows and increasing cross-ventilation through the building. The behavior of the building occupants will also affect the transmission potential of contaminants within the building, for example through opening windows, doors, or altering the ventilation rates of the rooms [28,34].
Filtration: Excluding and filtering BWA from entering the indoor air can be enabled using a filtration system installed in the HVAC system [7,13,16]. HVAC systems can contain filters of varying grades, which filter particles from the air as it passes through the HVAC system. While increasing the efficiency of the HVAC filter can lead to an increase in the indoor air quality, and exclusion of potentially hazardous particles from the indoor air, the increased efficiency may only be significant for particles within a certain size range and physical states. Most HVAC systems are not equipped with the fan capacity or the frame system required to install highly efficient filters, and upgrading the HVAC filtration system needs to take into account the potential increased loss of pressure through the system, which can lead to reduced airflow, increased HVAC power consumption, and poorer ventilation. Furthermore, leakage within the HVAC system may mean that the increased filtration provided by the more efficient filters may not result in an increase in the indoor air quality. Filters will require changing every year to 18 months depending on the pressures used and the type of filter, and need to be fitted by an HVAC expert so that there is no air leakage [7].
Deactivation: There are a number of air cleaners which can be either installed in an HVAC system, installed outside the HVAC system in the indoor environment, or used as portable units that can be moved about as required. These systems can include for example Ultraviolet Germicidal Irradiation (UVGI) systems, Photocatalytic Oxidation (PCO) Cleaners, and Ozone systems.
UVGI systems are often used to disinfect indoor air in both portable units and integrated into HVAC systems. These systems use ultraviolet light to disinfect the indoor air, with the system’s ability to clean the air dependent on the velocity, temperature, and Relative Humidity (RH) of the air. Units are typically installed in ducts of the air handling units (so-called in-duct), or on the ceiling or walls so to direct light upwards and not towards anyone inside the room (upperroom). Enhanced Ultraviolet Germicidal Irradiation (eUVGI) systems have been installed in hospitals and clean rooms as part of the HVAC systems, and have shown minimal benefits over High Efficiency Particle Air (HEPA) filters [7]. There is a lack of information on the effective use of UVGI systems, and the effectiveness of the UVGI deactivation appears to depend on the irradiation time, and therefore the ventilation rate [35].
PCO cleaners use Ultraviolet light and a photocatalyst to generate a photochemical reaction, leading to the creation of hydroxyl radicals which can oxidize pollutants. Typical catalysts include TiO2, WO3, ZnS, while the photocatalytic reaction can be achieved with fluorescent or UV light. Combination PCO/HEPA filter units have been proposed to purify the indoor air [36]. Pathogens have been observed to be readily destroyed by PCO units [37], however most research into PCO cleaner for indoor air purification have been trialled in laboratory settings, and there is little information available on its efficiency in a biodefense setting environment.
Ozone systems work by generating ozone, and dispersing the ozone into occupied spaces. Ozone has been shown to be effective against both Gram-negative and Gram-positive bacteria. However, there are known health impacts of ozone. Those exposed to ozone at concentrations over 0.2ppm for over 15 minutes have been observed to have respiratory problems, at which concentration ozone is ineffective at reducing indoor contamination [38,39]. Ozone can be used in high concentrations in indoor environments to decontaminate infected rooms, although its effectiveness is impacted by the relative humidity, and ozone can react with materials such as rubber [40,41].
Transmission: There are a number of protection measures that can be put in place to prevent further pathogen transmission from the contaminated environment and between building occupants. These are mitigation measures and act to minimize the human health impact of an attack.
Evacuation, Isolation, and Separation: Following an attack, individuals will need to be evacuated or sheltered in a safe location within the building, whilst keeping those who may have become infected separate and isolated from the non-affected population. An emergency plan should be developed for buildings at risk of an attack, with emergency procedures planned for indoor releases of BWA. Evacuation routes should be planned such that the routes follow paths with ventilation systems independent from the areas of the building where an attack may have occurred [14,15,29].
Isolation zones can be used to prevent the spread of BWA through a building. Isolation zones can be created in buildings by restricting airflow to and from the rooms where the pathogens are expected to be concentrated. Rooms of mail and personnel entry can be isolated from the rest of the building, ensuring that any BWA released in these areas do not spread through the rest of the building. Isolation zones can also be used to isolate specific locations within the building from contaminant exposure if a BWA is released elsewhere. Isolation zones can be created through the design of the HVAC system, and by minimizing the amount of airflow through gaps under doors and cracks. Isolation zones can also be established by using pressure differentials to ensure unidirectional air movement, as can be observed in hospital operating theatres and clean rooms. By ensuring that the airflow enters vital rooms through a highly filtered HVAC output and leaves due to pressure differences from the surrounding rooms, it is possible to keep the air cleaner than it would normally be. Self-contained filtration and air cleaning systems are available which can be installed in buildings to allow occupants to Shelter-in-Place (SIP) in the event of a bioterrorism attack. Safe rooms are commercially available which have been designed for chemical, biological, and radiation attacks.
Separation of contaminated or infected individuals from the unaffected population is likely to raise a number of ethical issues, which have been addressed elsewhere [42]. However, to protect building occupants during isolation or evacuation, a system of separation should be employed in order to minimize the further spread of infection.
Contact Tracing and Control: Contact tracing and control refers to the identification and diagnosis of contaminated or infected individuals based on tracing those who may have been in contact with an infected person, and has been demonstrated to prevent the spread of infection in a simulated smallpox outbreak [43]. Contact tracing can be used to identify how infections in indoor environments are spread from a source case to other within a building based on the work location of the original contaminated individual, or his movements throughout the building. In the case of bioterrorism defence, knowledge of those who work in areas that have been directly exposed to a BWA can be used to isolate these individuals to avoid further spread. Having an account of an infected individual’s movement throughout the building following an attack, for example based on their use of a security card, can help trace the potential extent of an infection following an attack due to person-to-person infection.
Personal Protective Equipment (PPE): Personal Protective Equipment (PPE) can be provided to all individuals working within the building in order to help limit the morbidity and mortality inside an attacked building. Respirators are effective means of minimizing the potential for morbidity and mortality in a population exposed to an aerosolised BWA. Protective respiratory devices can be classified as a Self-Contained Breathing Apparatus (SCBA), Supplied Air Respirator (SAR), and Air Purifying Respirators (APR). SCBA masks use a full face mask connected to a portable source of compressed clean air, and offer the highest level of protection. SAR respirators are linked to an air source through an airway, meaning the source of air remains separate from the contaminated air. APR are respirators which purify or filter the contaminated air, and can include full-face masks or surgical masks. Universal-fit respirators are available that form a seal at the users neck, protecting the user from a wide range of contaminants. These respirators can be stored at various locations throughout the building, and can have a shelf life of around 5 years. Disposable respirators are also used to prevent spread of diseases. EU standard EN149:2001 FFP3 or higher filtration respirators are recommended in healthcare settings when there is reason to believe a patient has a highly infectious disease [44]. Respirators of higher filtration such as Multi-layered HEPA filters are also available. Gloves may also be provided in order to minimize infection through direct contact with a contaminated surface.PPE are cheap, easy to use, and can be stored locally in the building making them quick to access. However, without the existence of a detect-towarn system, building occupants are unlikely to wear their PPE, and may become contaminated and infected.
Communication: Communication in this sense refers to the need to communicate the situation to individuals within the building, who are the victims of the attack, as well as to establish and maintain contact with external authorities who can take action in order to minimise further internal and external transmission and loss-of-life following an attack.
Internal Communication: Internal communication amongst those affected by the attack is critical in order to monitor symptoms of infection, and prevent further spread of the disease throughout the population [7,15,19]. By keeping the building occupants informed as to what has been suspected to have happened, and what is required of them in order to prevent further exposure, it may be possible to keep casualties to a minimum. A well-rehearsed evacuation or sheltering plan is critical for limiting the damage and chaos from an attack and identifying responsibility among the management team. As shown above, the success of some of the protection measures is heavily reliant on how people respond to the attack, and if the measures are implemented correctly at the critical time and space. At present, different protection measures may be installed in a building without proper organization and classification of their role and function. A systematic framework to classify different protection measures and their functions will help the emergency response by the management team.
External Communication: Following a bioterror attack, communication with external bodies is critical in order to limit the spread of contamination and infection through the wider population as well as to report the incident and request emergency response and other support to guide the building management. First responders, health protection bodies, and government officials need to be informed about the incident as detailed as possible in order to respond appropriately. This is similar to a fire incident in buildings. Understanding the building design and operation as well as the equipped fire safety measures and equipment can facilitate the emergency response. The framework proposed by this study can systematically and immediately informs the protection measures in the attacked building. If this framework is used as a general practice and a common language in the biosecurity field, it will help rescue workers and other professionals to decide the appropriate response strategy specific to the type of biosecurity system of the building such as to assess the extent of bioaerosol dispersal and the risk of exposure to the agents at different locations [24,28].
Investigation: Forensic investigation following a bioattack can be used to identify the method and extent of the attack, the BWA involved, and to identify the perpetrators. This information is crucial not only for presenting the case to the legal system but also to prevent and disrupt further attacks in other buildings. Investigation may involve using biosensors and environmental microbiological sampling techniques to determine the type of BWA used, while laboratory analysis can be used to learn more about any unique characteristics of the BWA [1]. Understanding more about the BWA such as genetic manipulation or cell membrane chemistry may help establish the capabilities of the offender and the provenance of the BWA. Forensic investigation should be carried out in full PPE, and with appropriately trained staff. Understanding the types of protection measures operating in the building will also facilitate the forensic investigation, for example the likelihood and requirements of using different entrances to release the BWA to the building. Moreover, if the building has a filter system in place in the ventilation system, BWA are likely to be captured by the filter and can help the investigation process. Investigation of the BWA and exposure levels is also critical for the efficient and effective treatment of victims of the attack [15,19].
Remediation: Following an attack, a building must be decontaminated and recommisioned in order for the building to become safe. Decontamination involves killing all BWA left inside the building, while recommissioning involves returning the building to an operational state.
Decontamination: An efficient and effective decontamination relies on appropriate sampling, testing and analyzing protocols in order to determine the presence of a BWA, and the extent and level of contamination. In addition, the building configuration, the mode of the bioattack and the existing biosecurity measures will influence the selection of the decontamination method [30]. Following sampling, containment and mitigation will prevent the BWA from being spread through re-aerosolisation or through newly infected individuals. Decontamination and subsequent validation monitoring then kills the remaining BWA within the building, and tests for any lingering contamination, respectively. Following the anthrax attack in 2001 in the United States, decontamination was completed to a “zero standard”, meaning that no viable anthrax spores could be detected inside the building [45].
Sampling a building for BWA contamination can be performed using disposable assays, or through laboratory analysis of swabs taken from the building. The sampling strategy should take into account the estimated dispersal of the BWA throughout the building, ensuring that the amount and extent of the contamination is fully understood. The protection measures used for contaminant identification and determining the extent of the dispersal are required for forensic investigation and detection.
Systems and technology for building decontamination have been developed in order to be able to quickly remediate a contaminated building. Decontamination generally takes the form of volumetric decontamination, where the volume of the building is decontaminated using either fumigation or a vaporous decontamination material such as hydrogen peroxide, surface decontamination, where liquid decontaminants and sporicides are applied to the surfaces inside the building, a hybrid application of both volumetric and surface decontamination, or leaving the building to become safe through natural microbiological decay. The selection of the disinfectant will depend on the BWA present, and the nature of the materials within the building construction. Reviews of the effectiveness of different disinfectants on BWA were developed by the Environmental Protection Agency (EPA) [46].
During decontamination, it is usual to place coupon samples throughout the building with a known quantity of BWA on them in order to compare the counts following the decontamination effort and assess the results.
Recommissioning: Prior to recommissioning the building, more samples should be taken throughout the building to ensure that the building is safe for re-occupation. Sampling should take into account the known extent of the contamination, and known “hot-spots” within the building. Understanding the protection measures in the building can assist in identifying and prioritising these critical points and shorten the time and effort for both decontamination and recommissioning of the building and increase building resilience to an attack.
Constructing and Assessing a Building-Specific Biosecurity Network System Based on the Proposed Framework
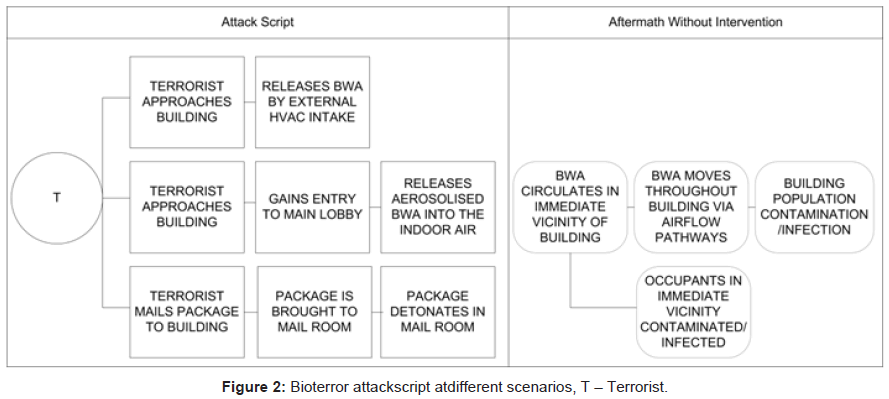
The protection measures discussed above differ in terms of their overall effectiveness, the part of the attack sequence they impact on, and their inter-dependencies. Figure 2 showed three scripts of bioattacks. Different scenarios can provide useful case studies to compare and validate biosecurity design options, which will be functional and compatible to other measures in the attack and protection sequence. Understanding how the protection measures interact spatially and temporally is necessary to determine the overall resilience of a building to an attack. The inter-relation of the different components of the framework is important; for example, an efficient alert and warning system is not effective unless there is a means of detecting the attack in the first place. Moreover, protection measures based on communication, control and targeted preventive actions are reliant on knowing that the building is under attack. Conversely, implementation of highly effective detection systems is likely to cause various ethical and incident management issues, if effective protection measures are not in place to respond to the potential attack.
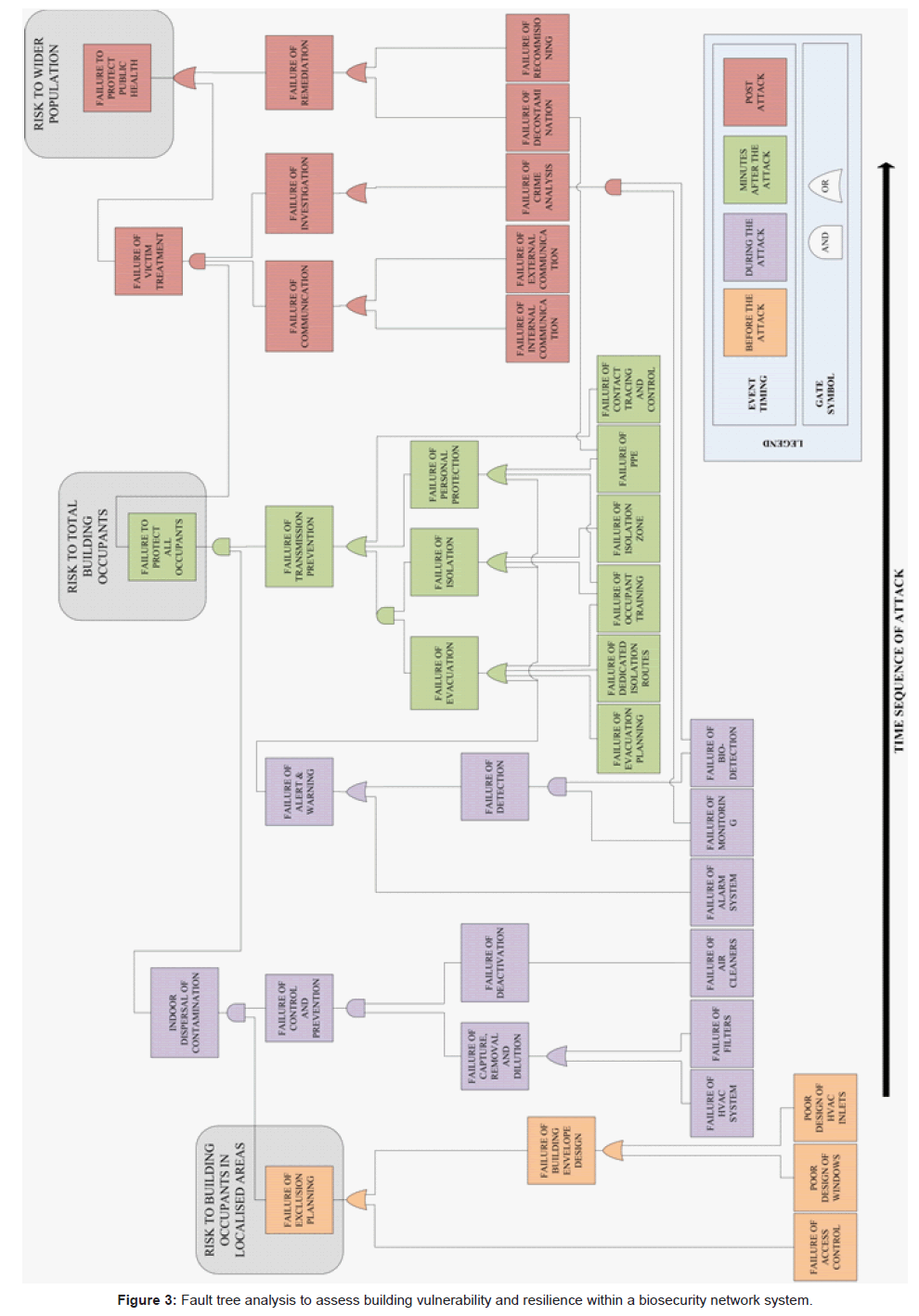
The inter-relation and inter-dependency of the different protection measures can be further described using a fault tree analysis (Figure 3), where the failure of a certain element of the protection measure framework can be related to the overall performance of the system [26]. Outcomes of an attack are considered to be either: local infection risk, where access to the building is gained and those in the immediate vicinity are contaminated and infected; whole building infection risk, where the BWA is able to travel around the building infecting the total building population; or an infection risk to the wider population, where the BWA poses a risk to those outside of the building. The assumption is that if offenders gain access to the building, the attack is likely to be successful in the immediate vicinity, and failure of the protection measures will prevent the attack from being contained, leading to an infection risk to all building occupants and potentially the wider population. The proposed failure network uses Boolean operators to represent whether a failure occurs if at least one of the protection measures fails (OR) or if all protection measures must fail for it to occur (AND).
To describe the impact of protection measures on a building, the different protection measures can be evaluated from most to least effective in terms of their probability of failure to perform given functions. The rough classification shown in table 1 was elicited from the literature cited in this study, and represents an initial description of the relative utility of different protection measures that maybe implemented in buildings, and acknowledges the current technological limitations of the protection measures. For example, detection and alert and warning protection systems are not currently publicly available with capabilities that would allow for a detect-to-warn system, meaning that the probability of failure to perform this function is high. Conversely, for other functions, such as exclusion, there exist a range of protection measures that are sufficiently developed to allow for a high level of protection against an attack, thus reducing the probability of success. Despite the lack of quantitative measures for the effectiveness of many protection measures, table 1 can be used as a reference point in conjunction with figure 3 for a qualitative risk assessment.
| Probability of Failure | Exclusion | Detection | Alert & Warning | Control & Prevention | Transmission | Communication | Investigation | Remediation |
|---|---|---|---|---|---|---|---|---|
| Low | Highly restricted access to building, for public No external access to HVAC vents or building systems | Fast-reacting biosensor network High biosensor sampling rate Training security personnel | Bioattack-specific alarm, linked to detection system | HVAC Purge System HVAC High performance filters and air cleaners Separate ventilation systems for public areas, the main building, and escape routes | PPE available to all occupants Planned escape route with separate ventilation system Contact tracing and seating data to identify exposed individuals | Established protocols for communication Emergency numbers for appropriate organisations Communication through media/press conferences | Access to laboratory for BWA analysis Highly trained staff PPE | Highly trained staff PPE Tested sampling methodologies Appropriate decontaminant methodology |
| High | Easy access to building Ventilation inputs accessible from ground level No screening of mail or packages | No trained security staff or biosensors | No bioterror-specific alarm system | Ventilation system without filters or air cleaners High degree of HVAC mixing Poor ventilation rate Building fully linked by single HVAC system | No PPE, no designated escape route Escape requires moving through attacked zone | No established communication protocols for dealing with bioattack Unclear communication/inconsistent advice | No access to appropriate lab facilities Untrained staff Inappropriate PPE | Untrained staff Inappropriate PPE Inappropriate sampling methodologies Inappropriate decontamination techniques |
Table 1: Examples of failure probabilities for the protection measures in the building vulnerability and resilience assessment.
The ability of the systems described in the framework to prevent a bioattack or reduce its consequences depends on the way protection measures are implemented. Protecting a building will require understanding the inter-relation between the components of the building protection framework, recognizing where current technology does not provide adequate capability, and strengthening other protection measures in order to counteract a bioterror attack. This proposed network system provides a platform for evaluating the relative efficiency of different protection measures, assessing their overall importance, and quantifying the overall resilience of a building to a bioattack. Quantitative data describing the effectiveness of every protection measure in the framework for each type of building is not available, however a building manager or a designer can use the network system to assess the vulnerability and resilience of a building and the risks of a successful attack and the responses required.
Despite research into the area of biodefense, vulnerabilities still exist in protection measure technology that may allow an attack to be successful. Future work will be performed in order to determine quantitative values for assessing the protection measures within the framework, allowing the resilience of a building to a bioattack to be evaluated in existing buildings. Using fault tree analysis within a building specific network system, an overall scoring system for building resilience will be developed. This system will allow for building resilience to be assessed according to the protection measures in place during assessment. When combined with an understanding of contaminant transport around buildings, building design, and occupant behavior, this network system can be used to plan and installed defenses to greatly reduce the probability and impact of a bioterror attack.
Conclusions
This paper has introduced a novel framework for the analysis of the vulnerability and resilience of a building to bioterrorist attacks, and discussed how much of the current technology available to protect a building from a bioterrorism threat fits within the framework. In addition, a fault tree diagram linking the different protection measures in the proposed framework together in order to demonstrate their inter-relation, inter-dependency, and the relative importance in the time-sequence of an attack has been proposed. Further research on quantifying the effectiveness of different protection measures employed in buildings will allow for the assessment of the vulnerability and resilience of a building. This work will help to improve the quantification of the vulnerability of existing buildings, and provide information to architects, builders, and building managers on how to best protect their buildings from, during, and following an attack.
Acknowledgements
The research leading to these results has received funding from the European Union Seventh Framework Programme FP7/2007- 2013 under grant agreement n° 242497. ZN is funded by EPSRC Grant Reference: EP/G029881/1.
References
- Lengel A (2005) Little progress in FBI probe of anthrax attacks. The Washington Post, USA.
- Graham B, Talent J, Allison G, Cleveland R, Rademaker S, et al. (2008) World at risk: Report of the commission on the prevention of WMD proliferation and terrorism. Commission on the Prevention of WMD Proliferation and Terrorism, New York.
- Kramer A, Schwebke I, Kampf G (2006) How long do nosocomial pathogens persist on inanimate surfaces? A systematic review. BMC Infect Dis 6: 130.
- Renfroe NA, Smith JL (2011) Threat/vulnerability assessments and risk analysis. Whole Building Design Guide, Washington, DC.
- Bossi P, Garin D, Guihot A, Gay F, Crance JM, et al. (2006) Biological weapons. Cellular and molecular life sciences 63: 2196-2212.
- Zilinskas RA, Hope B, North DW (2004) A discussion of findings and their possible implications from a workshop on bioterrorism threat assessment and risk management. Risk Anal 24: 901-908.
- Kowalski WJ, Bahnfleth WP (2002) Immune building systems technology. McGraw-Hill, New York.
- Reddy TA, Fierko J (2004) Uncertainty-based quantitative model for assessing risks in existing buildings. ASHRAE Transactions 110: 217-231.
- Radosavljevic V, Belojevic G (2009) A new model of bioterrorism risk assessment. Biosecur Bioterror 7: 443-451.
- Radosavljevic V, Belojevic G, Jovanovic L (2012) A mathematical model of bioterrorist attack risk assessment. Journal of Bioterrorism & Biodefense 1: 114.
- Ezell BC, von Winterfeldt D (2009) Probabilistic risk analysis and bioterrorism risk. Biosecur Bioterror 7: 108-110.
- NIOSH (2002) Guidance for protecting building environments from airborne chemical, biological, or radiological attacks. National Institute for Occupational Safety and Health, Cincinnati, US.
- NIOSH (2003) Guidance for filtration an air-cleaning systems to protect building environments from airborne chemical, biological, or radiological attacks. National Institute for Occupational Safety and Health, Cincinnati, US.
- LBLN (2005) Advice for safeguarding buildings against chemical or biological attack. Lawrence Berkley National Laboratory, US.
- ASHRAE (2002) Risk management guidance for health and safety under extraordinary incident. American Society of Heating, Refrigerating, and Air-Conditioning Engineers, Atlanta,GA.
- SBCCOM (2001) Basic information on building protection: strategies for protecting buildings from airborne hazards. U.S. Army Soldier and Biological Chemical Command, Washington, DC.
- USACE (2001) Protecting buildings and their occupants from airborne hazards. U.S. Army Corps of Engineers, Washington, DC.
- Chapman RE, Leng CJ (2004) Cost-effective responses to terrorist risk in constructed facilities. National Institute of Standards and Technology, Gaithersburg, MD.
- FEMA (2005) Risk assessment: a how-to guide to mitigate potential terrorist attacks against buildings. Federal Emergency Management Agency, US.
- USDD (2007) Unified facilities criteria (UFC): DoD minimum antiterrorism standards for buildings. U.S. Department of Defence, US.
- Thompson BP, Bank LC (2010) Use of system dynamics as a decision-making tool in building design and operation. Build Environ 4: 1006-1015.
- Thatcher TL, Wood EE, Edelson EC, Sextro RG (2005) Simplifying the assessment of building vulnerability to chemical, biological and radiological releases. Lawrence Berkeley National Laboratory, US.
- UTRC (2004) CBT-protection improvement design protocol-chem/bio: User’s guide. United Technologies Research Center, East Hartford, CT.
- RIDHO (2004) HVAC building vulnerability assessment tool. Rhode Island Department of Health Office of Occupational & Radiological Health, Rhode Island.
- Fielding JE, Schunhoff JF, Aguirre A (2006) BAC-Building assessment checklist protection against airborne hazards. County of Los Angeles Public Health, Los Angeles.
- Hope BK (2004) Using fault tree analysis to assess bioterrorist risks to the US food supply. Hum Ecol Risk Assess 10: 327-347.
- Reddy TA, Bahnfleth WP (2007) Requirements for a probabilistic quantitative relative risk-based decision methodology for reducing vulnerability of building occupants to extreme IAQ events. ASHRAE Trans 113: 281.
- Kobes M, Helsloot I, de Vries B, Post JG (2010) Building safety and human behaviour in fire: A literature review. Fire Saf J 45: 1-11.
- Beck VR, Yung D (1990) A cost-effective risk-assessment model for evaluating fire safety and protection in Canadian apartment buildings. Journal of Fire Protection Engineering 3: 65-74.
- CDC, NIH (2009) Biosafety in microbiological and biomedical laboratories. US Department of Health and Human Services, Washington DC, US.
- Nikoleli GP, Nikolelis DP, Tzamtzis N (2012) Portable biosensors for the rapid detection of biochemical weapons of terrorism. Springer, Netherlands.
- CMMPAS (Committee on Materials, Manufacturing Processes for Advanced Sensors) (2005) Sensor systems for biological agent attacks: protecting buildings and military bases. The National Academy Press, USA.
- Sreedharan P, Sohn MD, Nazaroff WW, Gadgil AJ (2011) Towards improved characterization of high-risk releases using heterogeneous indoor sensor systems. Building and Environment 46: 438-447.
- Taylor J, Lai KM, Nasir ZA (2012) Human factors and bioagent transmission following an indoor bioterror attack. Journal of Bioterrorism & Biodefense 3: 116.
- Hyttinen M, Rautio A, Pasanen P, Reponen T, Earnest GS, et al. (2011) Airborne infection isolation rooms–a review of experimental studies. Indoor and Built Environment 20: 584-594.
- Chuaybamroong P, Chotigawin R, Supothina S, Sribenjalux P, Larpkiattaworn S, et al. (2010) Efficacy of photocatalytic HEPA filter on microorganism removal. Indoor Air 20: 246-254.
- Pal A, Pehkonen SO, Yu LE, Ray MB (2007) Photocatalytic inactivation of Gram-positive and Gram-negative bacteria using fluorescent light. J Photochem Photobiol A Chem 186: 335-341.
- Berrington AW, Pedler SJ (1998) Investigation of gaseous ozone for MRSA decontamination of hospital side-rooms. J Hosp Infect 40: 61-65.
- HSE (2007) EH40/2005 Workplace exposure limits. Heath and Safety Executive, UK.
- Moat J, Cargill J, Shone J, Upton M (2009) Application of a novel decontamination process using gaseous ozone. Can J Microbiol 55: 928-933.
- Sharma M, Hudson JB (2008) Ozone gas is an effective and practical antibacterial agent. Am J Infect Control 36: 559-563.
- Borrion H, Mitchener-Nissen T, Taylor J, Ka-Man Lai (2012) Countering bioterrorism: Why smart buildings should have a code of ethics. Intelligence and Security Informatics Conference (EISIC), 2012 European 68-75.
- Eichner M (2003) Case isolation and contact tracing can prevent the spread of smallpox. Am J Epidemiol 158: 118-128.
- BSI (2001) EN 149: 2001:Respiratory protective devices. Filtering half masks to protect against particles. Requirements, testing, marking. British Standard Institution, London.
- EPA (2012) Homeland Security Research. Indoor and Outdoor Decontamination Research:9th October, 2012.
- EPA (2005) Compilation of available data on building decontamination alternatives. National Homeland Security Research Center, US Environmental Protection Agency: Office of Research and Development, Washington, DC.
Relevant Topics
- Anthrax Bioterrorism
- Bio surveilliance
- Biodefense
- Biohazards
- Biological Preparedness
- Biological Warfare
- Biological weapons
- Biorisk
- Bioterrorism
- Bioterrorism Agents
- Biothreat Agents
- Disease surveillance
- Emerging infectious disease
- Epidemiology of Breast Cancer
- Information Security
- Mass Prophylaxis
- Nuclear Terrorism
- Probabilistic risk assessment
- United States biological defense program
- Vaccines
Recommended Journals
Article Tools
Article Usage
- Total views: 21026
- [From(publication date):
December-2013 - Dec 17, 2025] - Breakdown by view type
- HTML page views : 16234
- PDF downloads : 4792